Aviation Math Is Elegant. Aircraft Maintenance Is What Keeps You Alive. A Comment on Encryption
Cyber algorithms are not the problem... how you build around them is
John Spiegel
2/27/20263 min read
Anyone who knows me will say I love planes. In fact, I was in tears at 10 years old when Dr Charlie Brown (yes, that was his name) told me I needed glasses. My dreams of becoming a fighter pilot died in those minutes.. But thankfully I found another profession…. So, let’s marry the two together!
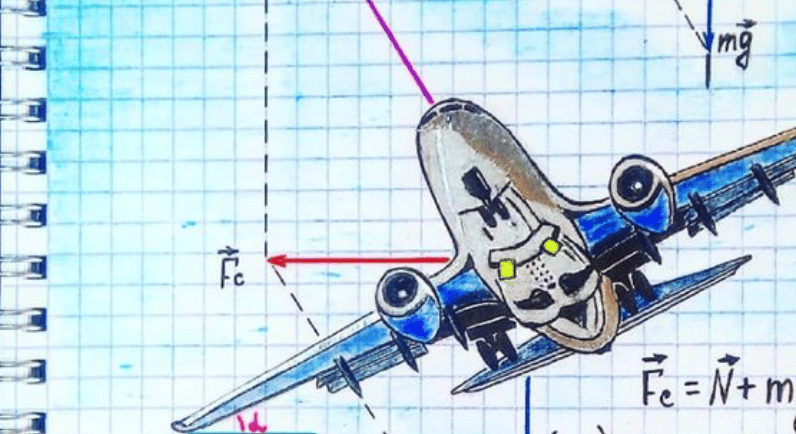
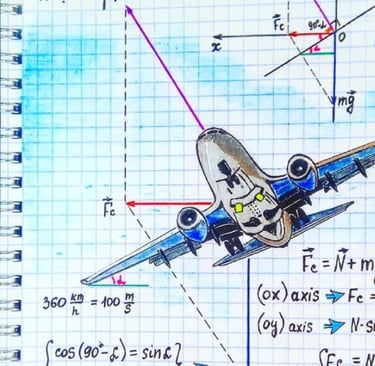
Modern aviation rests on extraordinary mathematics. Aerodynamic modeling, structural load calculations, propulsion dynamics, and control theory make sustained flight possible. The equations that govern lift and stress distribution are not in dispute; they are proven, refined, and deeply understood.
But aviation safety does not depend solely on mathematical correctness. It depends on engineering discipline. Aircraft are maintained under rigorous inspection regimes. Software controlling flight systems is developed under certification standards such as DO-178C. Every component is validated not only against expected behavior but against failure modes, edge cases, and environmental stress. The math makes flight possible. Maintenance keeps it safe.
Cryptography today faces a similar divide between theoretical strength and implementation rigor.
In February 2026, Trail of Bits published a sharply worded analysis titled “Carelessness Versus Craftsmanship in Cryptography.” The article draws a clear distinction between the rigor applied to cryptographic proofs and the far more inconsistent discipline applied to real-world implementations. The critique is not that modern algorithms such as AES, RSA, or elliptic curve schemes are broken. It is that the engineering translating those proofs into production systems frequently falls short.
The failure patterns are well known. Side-channel vulnerabilities remain prevalent despite two decades of research demonstrating how timing, cache access patterns, branch prediction, and power analysis can leak secret material. Constant-time implementation is not a theoretical nicety; it is a requirement when adversaries can observe microarchitectural behavior. Yet production libraries still contain data-dependent branches and memory accesses that expose timing oracles.
API design continues to be a structural weakness. Cryptographic libraries often expose low-level primitives directly, leaving nonce generation, parameter selection, and mode configuration to application developers. AES-GCM, for example, provides strong authenticated encryption guarantees, but nonce reuse catastrophically undermines its security model. ECB mode remains available in some contexts despite its unsuitability for structured data. Certificate validation logic is frequently implemented incorrectly, not because X.509 is broken, but because API ergonomics permit silent failure.
Testing practices also lag behind what would be expected in other safety-critical domains. Known-answer tests validate algorithmic correctness for predefined inputs but do not detect side-channel leakage, integer boundary errors, misuse scenarios, or adversarial edge cases. Property-based testing, coverage-guided fuzzing, and formal verification of critical paths remain inconsistently applied. In aviation, validation encompasses both nominal and failure conditions. In cryptography, testing often stops at functional equivalence.
Memory safety introduces another layer of risk. Cryptographic code written in C or C++ continues to expose buffer overflows, use-after-free conditions, and integer overflows capable of leaking or corrupting key material. The Heartbleed vulnerability was not a cryptographic failure; it was a bounds-checking failure in a library entrusted with protecting global TLS traffic. Memory-safe languages such as Rust demonstrate that performance and safety are not mutually exclusive, yet adoption remains uneven.
These implementation weaknesses matter because cryptography is foundational. It underpins TLS session establishment, certificate validation, token signing, secure enclaves, key management systems, and hardware security modules. In Zero Trust architectures, continuous verification depends on the assumption that cryptographic enforcement points behave exactly as specified. If the underlying implementation leaks secrets or permits misuse, the architectural model becomes fragile regardless of its theoretical soundness.
The stakes rise further as the industry transitions toward post-quantum cryptography. NIST’s standardization of lattice-based key encapsulation mechanisms and digital signatures introduces primitives that are more complex, larger in footprint, and less battle-tested than RSA or elliptic curve systems. Implementing schemes such as ML-KEM or ML-DSA requires careful attention to constant-time arithmetic, large polynomial operations, and resistance to microarchitectural leakage. If existing implementation habits persist, weak API boundaries, insufficient fuzzing, memory-unsafe defaults, and under-resourced maintenance, post-quantum libraries risk being quantum-resistant in theory yet vulnerable to classical exploitation in practice.
Post-quantum readiness must therefore include more than algorithm migration. It requires a disciplined inventory of cryptographic dependencies across the enterprise. It requires abstraction layers that prevent direct misuse of low-level primitives. It demands adoption of memory-safe implementations where feasible, comprehensive fuzzing that targets edge cases and adversarial inputs, side-channel analysis during code review, and independent audits before production deployment.
Aviation did not become safe because aerodynamic equations improved. It became safe because engineering discipline became institutionalized. Certification processes, inspection protocols, redundancy models, and failure analysis practices transformed theory into operational reliability.
Cryptography today does not suffer from weak mathematics. It suffers from inconsistent engineering discipline around that mathematics. As we approach the post-quantum transition, the distinction between theoretical strength and implementation rigor becomes decisive.
The equations get us airborne.
Craftsmanship is what keeps us in the sky.
